In the last quarter there have been a significant number of layoffs at high profile technology companies. The economy has also made these layoffs particularly challenging. If you didn’t receive a raise of at least 12% last year to keep up with inflation, then you didn’t get a raise or even got a pay cut. A job market flooded with candidates combined with top candidates seeking new positions means the job market is heating up for tech positions across the board. Some of these positions will be CISO level jobs and if you are in the market to make a career change you will inevitably run into salary negotiations at some point during the interview and negotiation process. Here are some things you will need to think about as a new or repeat CISO when negotiating for compensation in your new position.
Job Level
The management level of the CISO role varies across industry and company size. Some CISO roles are Director level, the majority are VP level (including Sr. VP and Executive VP) and a few are truly C-Level as named officers of the company. The role level should be commensurate with the level of responsibility – the more responsibility, the greater the impact to the company and the more senior the role should be. Likewise, the more responsibility, the more risk you are assuming (or responsible for) and so compensation should recognize and reward this.
Company Size
The first choice you will need to navigate is what type of company you want to work for. Public vs private companies will be the main tradeoff, but government or public sector may also be something else you are considering. The main thing to consider with company size is you typically can get a higher title at a smaller company, but this comes at the expense of a lower base salary or more risk in terms of the longevity and stability of the company or the ability to liquidate your equity. However, this risk comes with the potential for a bigger payout and so it is important to really do your research and make sure it is something you truly believe will succeed.
Government and public sector also offer interesting advantages. These roles can come with high visibility, but will typically offer lower salaries or total annual compensation than the private sector. The tradeoff here is you are forming highly visible connections across government and the public sector. You can also establish your reputation on a nationwide level. Lastly, government and public sector positions offer a pension or some form of retirement after the fact. Private sector companies typically do not offer the same level of retirement unless you self fund or have a match via an employer plan. There is a real tradeoff between private and public sector in terms of immediate compensation or deferred compensation, which will come down to your overall financial goals and associated timing.
Risk vs Reward
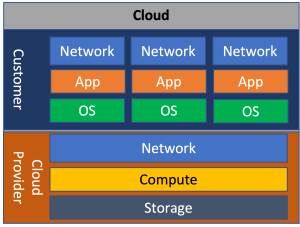
Let’s briefly talk about risk vs. reward. The type of company you choose to work for and the sector you choose to work in will dictate how much risk you are assuming, which will directly impact your compensation. On the one extreme there are startup companies. They offer the most risk, but also the most reward. On the conservative end of the spectrum there is government and public sector. These jobs are really stable, but can’t match the big pay offs that are associated with start ups or publicly traded companies.

In the graph above I placed public companies as having more risk than private companies due to the fluctuating nature of equity that typically makes up a large portion of the compensation at these companies. However, the real answer is “it depends” and so I encourage you to do your homework on the company you are considering.
Total Compensation
The next thing to understand is: what is the total compensation for the position and what makes up that total compensation? I often find interview candidates are hyper focused on base salary because it offers the guaranteed paycheck each month. However, there are a lot of other ways to build a total compensation package, especially at the executive levels. My recommendation is to take the time to understand all of the components that go into total compensation at the new role. Carefully evaluate the risks and to determine what you are comfortable with, then use that to discuss options with your prospective employer.
Cash Equivalents
Base salary is the big one here, but not the only one. This is the safest form of compensation because it is explicitly written in your offer letter and arrives at regular intervals. I will also lump sign on bonuses into base salary because they are typically granted when you start employment or are guaranteed payouts over a period of time (subject to remaining with the company for a specific term).
Annual Bonuses, Incentive Compensation Plans, Long Term Incentive Plans and Profit Sharing Plans are next on the list in terms of risk. These are basically cash payouts that are given at some interval (monthly, quarterly, semi-annually, annually) depending on the performance of the company. For example, if you are supposed to get a $100 bonus quarterly and in the first quarter your company misses their financial goals, they may choose to only finance 75% of the bonus amount and so you only get $75 that quarter.
Likewise, commission (if applicable) is essentially cash in your pocket, but assumes an amount of risk depending on your sales cycles, lead times, what vertical you are in, your customer, etc. CISOs who are in a public facing role at a product company may be eligible. Similarly, CISO Advisors who help drive sales may also be eligible for commission.
Commission is a lever you can pull on depending on how much risk you want in your compensation. Sales people typically carry very high commissions as percentage of base salary to incentivize them to get out there and sell. Sales engineers or indirect sales people typically have a much lower commission percentage as part of total salary.
Another common compensation option, particularly at public technology companies, is equity. Equity can come in many forms such as Restricted Stock Units (RSUs), Shares or Stock Options. All of these require some sort of sale to convert them to cash and their value will depend on the vesting schedule, how the company is performing, how the stock market is doing (if a public company) or the terms of your ownership in the company that specifies when and how you can sell your stake.
Equity is a form of compensation that allows the employee to assume an amount of risk in their total compensation and it ties their performance (and compensation) to the performance of the company. For a CSO this can be an incredibly rewarding form of compensation particularly if you help take a company through IPO or help mature a company to grow revenue or increase shareholder value.
All of these cash equivalents are negotiable, particularly things like amounts, vesting schedules, strike prices or even equity percentages. Whether or not you get some or all of these will depend on the company and job level of the role.
Indirect Compensation
Other things that will contribute to your paycheck are the benefits your company will provide. Here is a list:
- Healthcare – Do they cover healthcare, what type of plans do they offer and how much does the company cover? Do they have an on site gym or allow employees to expense gym memberships?
- Vacation / Leave – Does the company offer unlimited time off or are you limited to a certain number of weeks per year? What is the accrual rate, are there blackout periods, are there times when the whole company is expected to take off?
- Retirement – Does your company offer a 401k match and what other type of retirement investment options do they offer? Does your employer offer a deferred compensation plan, which can be useful as you approach retirement age?
- Training & Continuing Education – What type of training does your employer cover? Do they support you going to conferences? Does your employer offer tuition reimbursement or even pay for a full executive education program if you are considering going back to school? Do they cover professional memberships and certifications?
- Work Permits / VISA Sponsorship – Do you require and does your prospective employer offer VISA sponsorship?
- Relocation Assistance – Do they offer relocation assistance if you are being asked to move? What type of accommodations and support will they provide if you are being asked to move to a foreign country?
- Travel & Expense Policies – What type of travel policies do they have when you travel? Do they provide you with a cell phone or allow you to expense your current phone and plan? Do they pay for your internet connection if you are a remote employee? Do they cover mass transit passes or parking (if located in a major city)?
- Discounts & Perks – Do they offer employees other perks like discounts, free tickets to sporting events or awesome swag?
All of these options will vary depending on the company you are considering and it is important to ask questions and consider all of these additional benefits that will indirectly boost your paycheck.
Other Things To Consider
When negotiating for your new CISO role, there are other things you may want to consider asking for depending on your job level and amount of responsibility.
First, you will most likely want to negotiate a severance if you are laid off or terminated as a result of a security event. Typical severance packages offer some amount of base salary payout, but can also include accelerated vesting schedules, guaranteed bonuses, relocation, cash payouts, etc. Severance packages typically don’t come into play until the more senior levels, but given the high risk nature of the CISO role it is something to ask about during the interview or salary negotiations.
Second, if you are in the senior management ranks it is important to ask if the role is going to be a named officer of the company. If it is, you will want to ask about being included in the liability policy for Directors and Officers. If not, you may want to ask if the company has a standard corporate liability policy and if you can be included in it, which can help protect you during lawsuits or other legal issues you may encounter while employed in the role. You may also want to negotiate for the company to cover your legal fees if you are sued and have the ability to select and retain legal counsel of your choosing that the company pays for, but represents you.
This brings us to the last point of consideration which is contracts and contract terms. At the more senior ranks it is typically to negotiate for all these things, but agree to stay for some period of time as specified in an employment contract. This contract may also have specific non-compete agreements, specific non-disclosure agreement terms and other terms you may have negotiated. They key takeaway is to get everything that has been agreed to in writing and included in the contract.
Wrapping Up
Salary negotiations can be stressful, but they don’t need to be. Doing research, asking questions and knowing your worth can help make salary negotiations go smoothly. Some states now have pay transparency laws which can make it easier to understand the compensation range for the role. At the higher employment levels you may want to consider retaining a compensation lawyer who can draft and review contract or compensation terms on your behalf. Not all of the options I’ve mentioned above will be available at your employer or at the job level you are applying for and so taking the time to understand what is available is important to make sure you are being compensated and protected appropriately.